Contents
What Is a 51% Attack?
First of all, make sure to read the article about orphan, stale and uncle blocks in Bitcoin and Ethereum mining.
Let’s say a miner owns 60% of the network hash rate. This lets him “hold” his blocks and not send them to the network. Instead, he continues mining his own chain by himself. Over a certain period of time, the miner is very likely to create more blocks than the rest of the network. As a result, the miner’s chain becomes longer, so when he puts it out into the world, the network gladly accepts it, while other miners keep mining and get nothing for found blocks because all of their blocks have become orphan and/or stale.
2019 – Biggest Ethereum Classic Hack
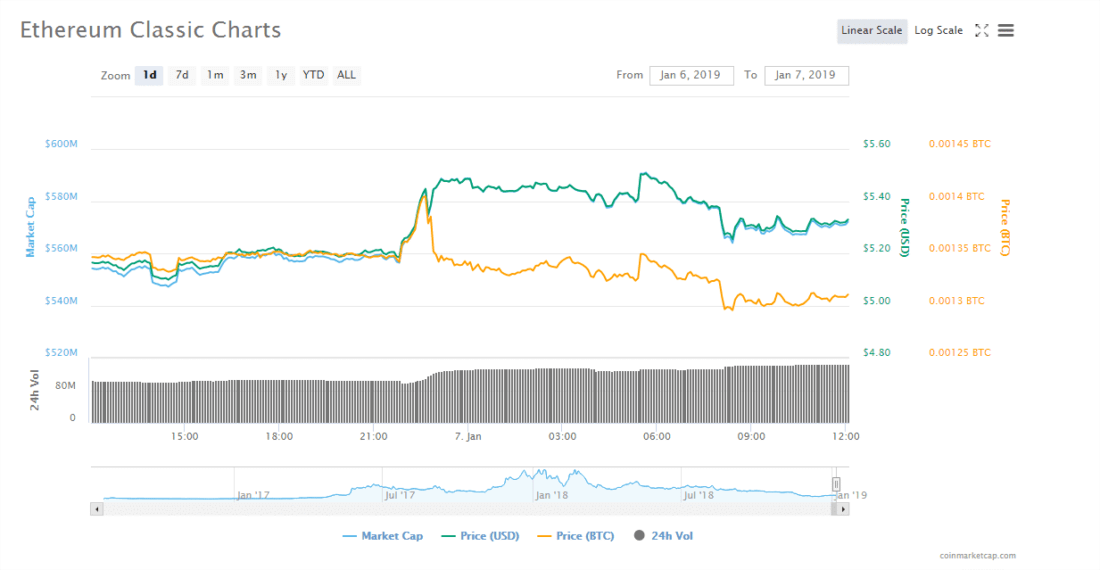
It seems that rumors about the ETC chain reorganization and double spend attack turned out to be true. Blockchain ecosystem security company SlowMist was the first to report the issue. In the course of a few hours, the blockchain went through several reorganizations, which was confirmed by an Ethereum Classic BlockScout block explorer. The Ethereum Classic team informed exchanges and mining pools about the need to increase the number of block confirmations.
Previously, Coinpage reported that Ethereum Classic is under a 51% attack. After that, exchanges that trade the coin were notified about the potential threat and the need to upgrade their security. The news caused the ETC exchange rate to drop.
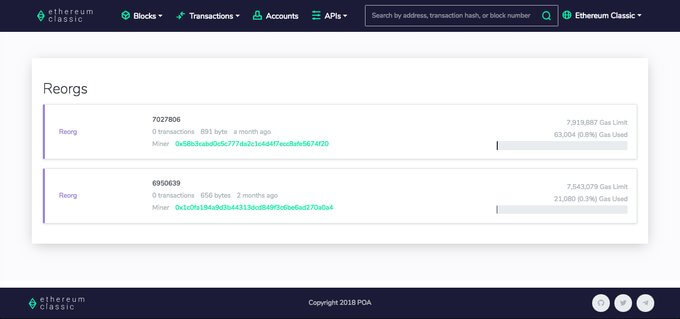
However, the official Ethereum Classic speaker tweeted that they are not aware of any double spend attack or chain reorganizations attaching the screenshot to back up his remarks.
There have been rumors of a possible chain reorganization or double spend attack.
From what we can tell the ETC network is operating normally.
BlockScout's "Reorg" section shows nothing of the sort.https://t.co/Yi2cXusCz9 pic.twitter.com/HdUtS0DJZK
— Ethereum Classic (@eth_classic) January 6, 2019
There is no doubt that the chain reorganization did happen, probably after the tweet. The next tweet by Ethereum Classic only fueled more rumors. In the tweet, exchanges and mining pools were informed about the need to increase transaction confirmation time and set a minimum limit for coin deposits and withdrawals.
Before that, an unknown user bought hashing power on Nicehash to mine Ethash based coins, which caused the platform’s prices to double. MiningRigRentals was also used for the attack. As a result, the hacker managed to gain control of the chain.
2Miners Ethereum Classic Pool Operation during the Attack
2Miners increased block confirmation times as recommended in both pools: PPLNS and SOLO.
Ethereum Classic (ETC) blockchain is under attack.
Confirmation time is increased to 200 blocks at the moment for ETC pools.
We will keep you updated. pic.twitter.com/UIMQ7UK55s— 2Miners (@pool2miners) January 7, 2019
How Can You Take Advantage of a 51% Attack?
Let’s say, you are the bad guy who owns 60% of the network. You have 100 BTC in your wallet. You are mining and making your chain grow longer, while nobody knows of its existence. Then you send 100 BTC to an exchange, but instead of doing that in your own chain, you use the chain that is accepted by the rest of the world. Your coins reach the exchange and receive confirmation. You exchange them for another cryptocurrency, let’s say Ethereum, and withdraw your coins from the exchange. Then you make your chain public saying something like:
“Sorry guys, the world’s chain sucks. Mine is longer, so it’s valid.”
The Ether is in your wallet. As for Bitcoin, you never actually sent it anywhere. As a result, the exchange bears a loss.
You should understand that if you own 51% of the network, you can’t possess, seize or destroy the network itself. You don’t have access to users wallets or transactions, neither past nor future.
Is it profitable? It depends on the coin. For example, it is surely not profitable to attack Bitcoin. It would require too much hashing power to do so, and therefore be too expensive, relative to the potential profit.
It isn’t only exchanges that run the risk of a 51% attack, but also any service that accepts cryptocurrency as a form of payment.
What Is An Attacker Unable To Do?
The miner that owns 51% doesn’t control anything. He is just a miner. He doesn’t have access to wallets. Without the private key to your wallet, nobody in the world can access it. The miner may mine blocks or he may not. Of course, there is a chance that he will roll back your transactions, but there is no way he can change the recipient of your transactions or send coins from your wallet on your behalf. You are the only person who can control your cryptocurrency.
The attacker can’t create new coins out of thin air, he can’t control anyone’s balance! It’s nonsense.
Why Doesn’t Anybody Attack Bitcoin Or Other Major Coins?
One should understand that if you were to attack one of the major coins, you would need to spend millions of dollars per hour. Not many people would spend this much money knowing that profits are not guaranteed.
For mining pools that own 51% of a coin’s hash rate, it’s even worse. If they try to defraud the community, they put their whole business at risk.
If a pool organizes a 51% attack, everyone will find out about it right away. The pool would be discredited, crypto developers and miners wouldn’t work with it anymore and the platform would cease to exist. Do pools really need that? They get a decent percentage from mining activity, so such a scenario is very unlikely.
Even if a pool conducts a 51% attack, crypto creators can just roll back their blockchains using hard forks. The DAO has already set a precedent for that.
How To Fight Against 51% Attacks
Exchanges require a great number of confirmations before crediting coins to the user’s balance. For example, ZEN or ZCL require as many as 500 confirmations, that is, 500 new blocks or 1,250 minutes, which is almost 24 hours! Too long, right? But it’s the only way networks with a low hash rate can protect themselves. This requires an attacker to spend more resources to obtain 500 blocks than it would be worth to perform the attack.
Pools are in control of what’s happening, they see the hash rate distribution among miners and who confirms which blocks. If a pool suspects something, its representatives will notify the community and cryptocurrency developers, so that they could roll back the blockchain and take further action if necessary.